Problem
You may want/need to create and enable a swap file on your machine. Many Linux distribution installers will create an extra partition for swap. However, there are several advantages to simply using a swap file on your root partition (the partition you installed Linux on). Here's a few:
- you can increase / decrease it's size much easier than resizing partitions;
- if you use LUKS for encrypting your root partition, then you either have to encrypt your swap partition to maintain security (swap can contain sensitive information and are exploitable) or you can simply use a swapfile on your root partition (which is then encrypted along with everything else on the root partition);
- If you encrypt your root partition AND your swap partition, then you will need to enter two decrypt passphrases (one for root and one for your swap partition) unless you also mount your LUKS swap partition with a keyfile (in which case you'll need to edit
/etc/fstaband/etc/cyrpttab) - for a swapfile you don't have to worry about any of that;
This tutorial covers setting up Arch (and Arch-based distros like Manjaro etc.) to use a swap file, enable hibernation, and cover a few things in the case of doing this on a LUKS root partition.
Solution
We'll cover the following:
| Table of Contents | ||
|---|---|---|
|
Create and enable swap file on root partition
We'll create a swap file on Arch-based distro via several terminal commands. Note, you'll need sudo access for all of this.
First let's check if any swap files (or partitions) are already in use:
| Code Block | ||
|---|---|---|
| ||
sudo swapon -s |
Output will list any swap files already active. To turn off all swap devices use:
| Code Block | ||
|---|---|---|
| ||
sudo swapoff -a |
On my machine I have 16GB or RAM and since I want to enable hibernation (using this swap file) I'm going to create a 17GB swap file (just to be sure if can store the entire RAM contents if needed). If you're not interested in using hibernation (i.e. suspend-to-disk) then you probably can use a smaller swapfile.
The following will create, secure (i.e. set safer permissions on), and enable a 17GB swap file at /swapfile
| Code Block | ||
|---|---|---|
| ||
sudo dd if=/dev/zero of=/swapfile bs=1M count=17408 sudo mkswap /swapfile sudo chmod 600 /swapfile sudo swapon /swapfile |
Making swap persistent
Doing the above will simply create and enable our swap file. After a reboot our swap file won't be enabled.
We're going to be editing /etc/fstab - which is an important file and messing it up could render your system unbootable. So let's first back it up:
| Code Block | ||
|---|---|---|
| ||
sudo cp /etc/fstab /etc/fstab.backup |
Now let's make our swap file persistent:
| Code Block | ||
|---|---|---|
| ||
echo '/swapfile none swap defaults 0 0' | sudo tee -a /etc/fstab |
Now make sure you run (see below) which will check for errors. If nothing (no errors) show then you should be good to go. If errors, don't reboot until you fix (or restore fstab from the backup we made).
| Code Block | ||
|---|---|---|
| ||
sudo mount -a |
If there is no error output, then we should be good to go and we can not delete the backup we made:
| Code Block | ||
|---|---|---|
| ||
sudo rm /etc/fstab.backup |
Enable hibernation
Let's first enable hibernation. On Arch-based distros , we're going to use a script which automates setting up hibernation. Install the hibernator package and run it as root:
| Code Block |
|---|
sudo pacman -S hibernator sudo hibernator |
Once the hibernator script has run you should have the requirements for hibernate to work.
Hibernator does update your grub config. It does a pretty good job in setting the resume and offset kernel parameters.
Updating grub
We're going to be editing /etc/default/grub. Note that there is scope here to mess things up royally. So, let's backup our current grub file to be safe(r)
| Code Block | ||
|---|---|---|
| ||
sudo cp /etc/default/grub /etc/default/grub.backup |
So, before we can edit our grub, we need a few pieces of information:
- device name of partition where have swap file;
- physical offset of
/swapfile(which is my swap file).
Find device UUID for root partition (non-LUKS)
For a standard (non-LUKS) root partition we need the partition that is mounted to root (/) and it's UUID.
An easy way to find the partition mounted to root is by running:
We're looking for "Mounted On" "/". In the example picture above, we can see that /dev/sda3 is mounted on "/".
To find the UUID for our partition we can run:
| Code Block |
|---|
blkid |
which will print out the UUID for each of our paritions. Make note of the UUID for the your root partition.
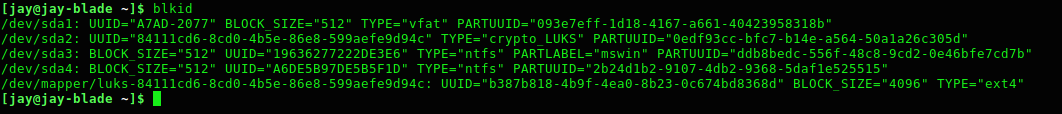
Find mapped device for LUKS root partition
If you have a LUKS root parition, the easiest way to find the line we're going to be using in our grub config is to run:
| Code Block |
|---|
blkid |
This will print out our partitions and their UUID. An example would be:
Since we know our root is LUKS encrypted, the mapped device ID that we want would be:
| Code Block |
|---|
/dev/mapper/luks-84111cd6-8cd0-4b5e-86e8-599aefe9d94c |
Find physical offset of /swapfile
We also need to the physical offset for our swap file. Grub needs this to know example where the swap file resides on the root partition. We can find this offset by running:
| Code Block | ||
|---|---|---|
| ||
sudo filefrag -v /swapfile |
For my system, running the above outputs:
The value we are after is the ext 0 physical offset (first value of physical_offset) as shown in the image (red rectangle).
Updating grub config to resume (hibernate) on boot
With these pieces of information let's now edit our grub config
| Code Block | ||
|---|---|---|
| ||
sudo vim /etc/default/grub |
We want to find the line starting with GRUB_CMDLINE_LINUX_DEFAULT and append following following bits of information we got previously.
For non-LUKS root partitions it should end up looking something like this:
| Code Block |
|---|
GRUB_CMDLINE_LINUX_DEFAULT="quiet resume=UUID=f68ed3c5-da10-4288-890f-b83d8763e85e resume_offset=45731840" |
For LUKS root partitions it should end up looking something like:
| Code Block |
|---|
GRUB_CMDLINE_LINUX_DEFAULT="quiet cryptdevice=UUID=84111cd6-8cd0-4b5e-86e8-599aefe9d94c:luks-84111cd6-8cd0-4b5e-86e8-599aefe9d94c root=/dev/mapper/luks-84111cd6-8cd0-4b5e-86e8-599aefe9d94c resume=/dev/mapper/luks-84111cd6-8cd0-4b5e-86e8-599aefe9d94c resume_offset=45731840" |
Now, we can save our changes and then run
| Code Block | ||
|---|---|---|
| ||
sudo update-grub |
Reboot and hibernation should *hopefully* now be working.
References
- https://confluence.jaytaala.com/display/TKB/Create+and+enable+swap+file+on+Linux
- https://wiki.archlinux.org/index.php/Swap#Swap_file
- https://wiki.archlinux.org/index.php/Power_management/Suspend_and_hibernate
Related articles
| Content by Label | ||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
|
| Page properties | ||
|---|---|---|
| ||
|